Changing fail2ban settings to block with pf
Hello, I'm incompetent. Today's article is about my utter incompetence.
Huh!? There's a strange log appearing in fail2ban.log!
Alright, alright, I thought I'd take a look at what fail2ban had banned... and then I saw this:
2024-07-24 20:52:43,027 fail2ban.utils [39963]: INFO HINT on 127: "Command not found". Make sure that all commands
in "{ iptables -w -C f2b-sshd -j RETURN >/dev/null 2>&1; } || { iptables -w -N f2b-sshd || true; iptables -w -A f2b-sshd -j RE
TURN; }
for proto in $(echo 'tcp' | sed 's/,/ /g'); do
{ iptables -w -C INPUT -p $proto -m multiport --dports ssh -j f2b-sshd
>/dev/null 2>&1; } || { iptables -w -I INPUT -p $proto -m multiport --dports ssh -j f2b-sshd; }
done" are in the PATH of fail
2ban-server process (grep -a PATH= /proc/pidof -x fail2ban-server/environ). You may want to start "fail2ban-server -f" separa
tely, initiate it with "fail2ban-client reload" in another shell session and observe if additional informative error messages a
ppear in the terminals.
Oh, it says a command is not found... And I completely forgot!!! In the case of FreeBSD, it's controlled by pf... For GNU/Linux, iptables is fine, but I was using BSD and completely forgot... So, I'll reconfigure it, referring to this site: https://dbdemon.com/pf_and_fail2ban. Since I'm using $exsrv1 for my own server,
# Fail2Ban
table <f2b> persist
anchor "f2b/*"
block drop in log quick on $exsrv1 from <f2b> to any
This is the setting. Wait, can it use regular expressions like f2b/*...? And then, I reconfigured jail.conf. I simply put it in the Default section.
[DEFAULT]
banaction = pf[actiontype=<allports>]
banaction_allports = pf[actiontype=<allports>]
[sshd]
enabled = true
port = ssh
logpath = /var/log/auth.log
bantime = 1w
findtime = 1d
maxretry = 5
[postfix]
enabled = true
port = smtp,ssmtp,submission
logpath = /var/log/maillog
bantime = 1w
findtime = 1d
maxretry = 10
[dovecot]
enabled = true
port = pop3,pop3s,imap,imaps,submission
logpath = /var/log/maillog
bantime = 1w
findtime = 1d
maxretry = 10
Looking at the configuration file, it's already set by default in action.d/pf.conf, and when I check it,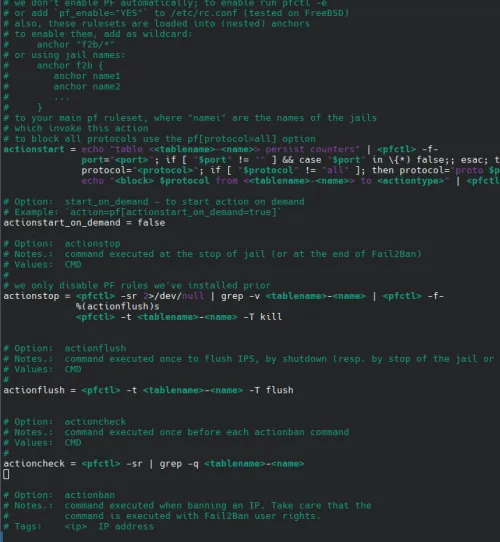
it seems I don't need to make any special changes to the command calls like this. So, after restarting fail2ban and pf and checking the fail2ban logs, it seems that the IPs that were banned before are carried over as they are.
# fail2ban-client status sshd
Status for the jail: sshd
|- Filter
| |- Currently failed: 1
| |- Total failed: 1
| `- File list: /var/log/auth.log
`- Actions
|- Currently banned: 37
|- Total banned: 37
`- Banned IP list: *
I'll observe it again with this.
Well then. Thank you for your continued support.